Product & UX Design
Emerging
technology,
made clear.
From GenAI and agentic workflows to enterprise platforms, I turn complex systems into interfaces that feel inevitable.
Work History
OracleCapital OneFireEyeNowSecure
Selected Works
Recent
Explorations
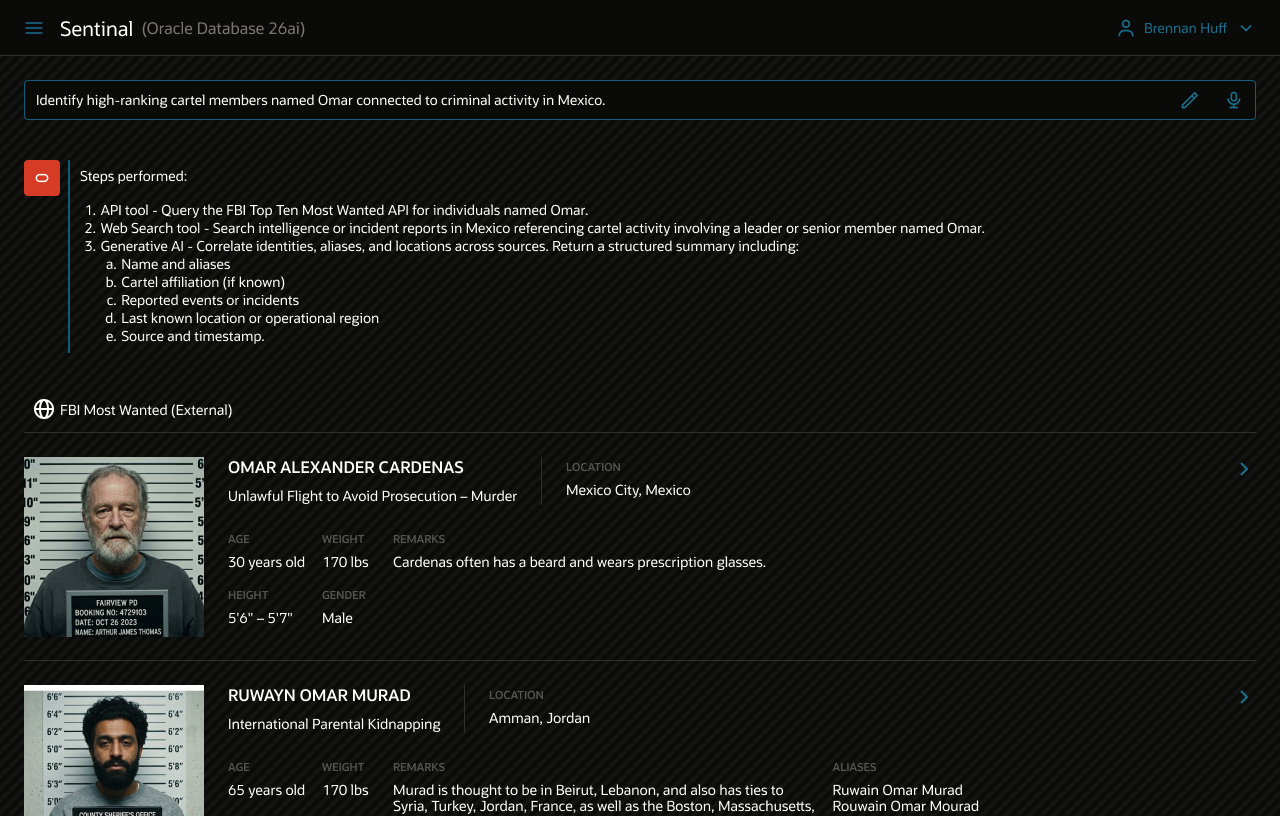
Enterprise AI, security platforms, and intelligence systems. 2022-2025.
Agentic AI is a systems orchestration problem, not just a model problem - security and clarity must be designed into the UX.
Profile
Designing at the edge of what's technically possible.
I design for the intersection of emerging technology and human understanding - building interfaces where AI agents, structured data, and real-time intelligence converge into experiences that feel precise, not overwhelming.
My process starts with possibility: explore what AI can do before constraining the design. Then scope, prototype with real models, observe actual behaviour, and iterate with deep attention to detail.